- Home
- /
- Product Review
- /
- BharOS: India’s Android Rival?
Introduction: The Geopolitical Imperative of Mobile Sovereignty
India’s digital landscape is characterized by its immense scale, hosting the world’s second-largest smartphone market. However, this vast digital ecosystem is underpinned by a profound dependency: nearly all mobile devices operate on foreign-controlled operating systems, primarily Google’s Android and Apple’s iOS. This technological reliance creates inherent national security vulnerabilities, raising concerns over data sovereignty, potential supply chain attacks, and the control of critical digital infrastructure by external entities. For a nation committed to safeguarding its burgeoning digital economy, the operating system is not merely utility software, but a strategic asset requiring domestic control.
The governmental response to this dependence is embodied in the ‘Aatmanirbhar Bharat’ (Self-Reliant India) initiative, which provided the impetus for the creation of BharOS. BharOS is a government-funded project intended for deployment in high-security governmental and public systems. Developed by JandK Operations Private Limited (JandKops), a non-profit firm incubated at the Indian Institute of Technology Madras (IIT Madras), the OS is officially positioned as a crucial step toward achieving technological independence and shifting the national digital foundation away from foreign technology reliance.
The Regulatory and Policy Backdrop
The public presentation and testing of BharOS by key Union Ministers, including Minister for Telecommunications Ashwini Vaishnaw and Education Minister Dharmendra Pradhan, aligns with a period of intensified governmental scrutiny over global technology monopolies. The announcement follows the Competition Commission of India’s (CCI) findings that Google had abused its dominant position within the OS market. BharOS thus functions as a non-monetary, technological counter-measure, designed to provide a real-world, government-sanctioned alternative, particularly for sensitive enterprise and communication platforms. This structural development offers the Indian government crucial leverage in ongoing and future regulatory engagements with global technology giants regarding platform dominance.
BharOS is strategically conceived as a piece of core digital infrastructure rather than a general consumer product. The core objective is national security: to mitigate geopolitical cyber threats and minimize external data leakage risks by shifting the fundamental root of trust from foreign entities to a domestically controlled and maintained foundation. This strategic imperative prioritizes controlled, high-assurance environments over the immediate goal of mass market adoption.
The BharOS Blueprint: Architecture, Features, and the Quest for Trust

BharOS is meticulously engineered to cater to organizations where security and rigid data control are paramount. Its architecture is fundamentally tailored to remove the common vectors of security and privacy compromise associated with widely deployed commercial mobile operating systems.
Foundational Architecture: AOSP Under the Hood
BharOS is technically a Linux distribution, based on the Android Open Source Project (AOSP), sharing its core kernel structure with the Android family of operating systems. It is developed to support the ARM64 platform and includes linguistic support for English (India), Hindi, Odia, and Punjabi.
The decisive architectural difference between BharOS and commercial Android lies in the complete absence of Google Mobile Services (GMS) and any pre-installed Google applications. This removal is the primary privacy enhancer, eliminating a major mechanism for widespread tracking and data exchange with foreign corporate servers. Furthermore, developers have claimed extensive customization to the core security protocols, including modifications related to the root of trust and chain of trust. These modifications suggest implementation of secure boot mechanisms, common to high-security AOSP derivatives, designed to guarantee the cryptographic integrity of the device software, starting from the secure hardware layer.
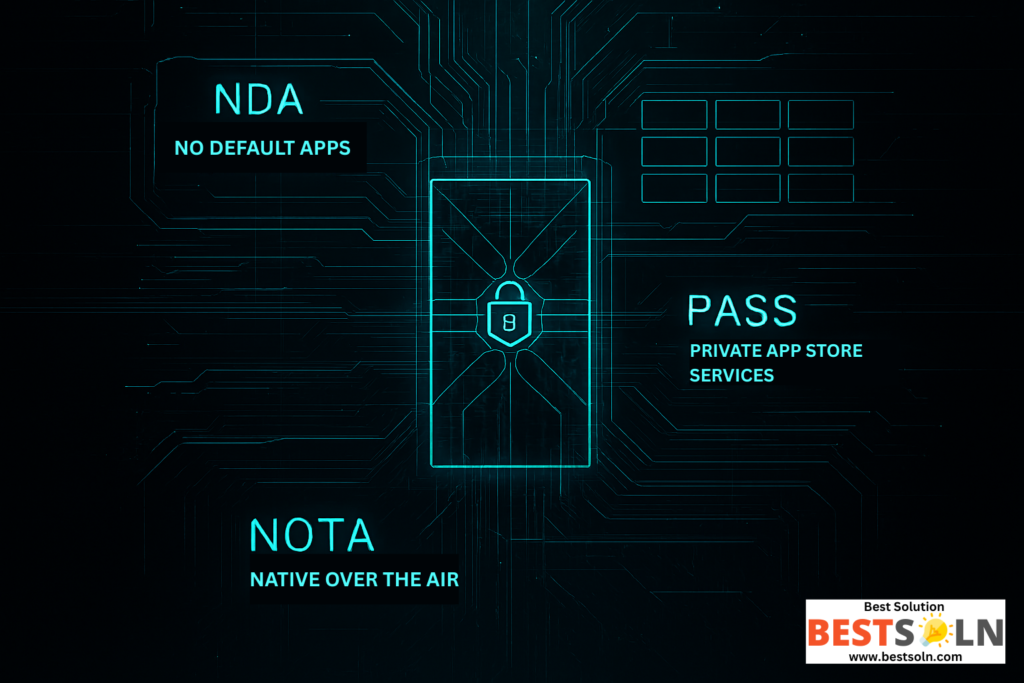
The Three Pillars of High-Assurance Security
The operating system’s security model is built on three core, mutually reinforcing features designed to maximize organizational control and minimize the device’s attack surface.
No Default Apps (NDA)
BharOS ships with No Default Apps (NDA). This feature instantly minimizes the system’s attack surface by eliminating unnecessary pre-installed applications or “bloatware.” By not forcing users to rely on potentially untrusted or unfamiliar pre-loaded applications, users gain enhanced control over app permissions, choosing exactly which applications are allowed to access specific device data or features.
Private App Store Services (PASS)
In sensitive deployment environments, the greatest security risk often arises from user behavior and the installation of malicious or unvetted software. To address this, BharOS foregoes a public app store in favor of organization-specific Private App Store Services (PASS). A PASS offers a strictly curated, thoroughly vetted list of approved applications that have demonstrably met the organization’s stringent security and privacy standards. This architectural feature acts as a controlled digital gateway, ensuring high levels of compliance and preventing the inadvertent introduction of malicious third-party software, confirming the OS’s design for organizational compliance and control.
Native Over The Air (NOTA) Updates
Maintaining high device integrity requires constant and reliable security patching. BharOS addresses this through Native Over The Air (NOTA) updates. NOTA updates are designed to be automatically downloaded and installed on the device without requiring manual user initiation. This mechanism ensures the device constantly operates on the latest secure operating system version, incorporating essential security patches and bug fixes, thus significantly reducing the vulnerability window against exploits.
It is important to recognize that successful BharOS deployment requires specific infrastructure. The intended target market often comprises organizations whose users handle sensitive information and require access to private cloud services, typically facilitated through dedicated private 5G networks. This requirement anchors the OS’s success to sophisticated, high-cost organizational infrastructure, confirming its status as a highly specialized enterprise tool and inherently limiting its applicability in the general consumer market.
Table 1: BharOS Core Security Features and Implications
| Feature | Description | Primary Security Benefit | Market Limitation |
| No Default Apps (NDA) | Ships without any pre-installed applications or bloatware. | Minimal attack surface; maximized user control over app permissions. | Requires manual sourcing and installation of essential utility apps. |
| Private App Store Services (PASS) | Organization-specific, curated, and vetted list of allowed applications. | Prevents installation of untested or malicious third-party consumer apps. | Excludes the vast majority of consumer applications and services (No GMS ecosystem). |
| Native Over The Air (NOTA) Updates | Automatic downloading and installation of security patches and bug fixes. | Ensures high device integrity and reduces vulnerability window. | Requires consistent network access and maintenance of the update server infrastructure. |
Dissecting the Claim: Integrity, Licensing, and the GrapheneOS Controversy

The claims of indigenous development and superior security have been challenged by technical auditors in the open-source community, placing a burden of proof on the BharOS development team.
The Core Allegation: A Cosmetic Fork
The most significant controversy stems from the allegation that BharOS is a “mere cosmetic fork” or derivative of GrapheneOS, an existing, highly regarded, security-focused open-source mobile operating system that is also based on AOSP. Technical inspection of leaked repositories suggested that the BharOS code resulted from a “simple ‘find and replace’ job” where textual references to ‘GrapheneOS’ were replaced with ‘BharOS’ across core components, including the Settings App, Camera App, and Frameworks Base. This finding stands in direct contrast to the claim by the director of IIT Madras that the team expended “1 year” developing the system.
This lack of demonstrated original development effort challenges the competence and integrity of the JandKops team. Claiming this derivative technology as fully ‘Aatmanirbhar’ is considered disingenuous by the open-source community because it effectively “invisibilises the labour and intellectual property” of the original open-source contributors.
Licensing Compliance and the Trust Deficit
Furthermore, the project faces scrutiny regarding its adherence to open-source licensing. While the GrapheneOS license permits the use and modification of its source code, it typically requires that the license itself be included in any modified redistribution. Critics allege that the BharOS repository “conveniently omitted” this critical licensing requirement, potentially placing the project in violation of open-source software licenses.
For an operating system intended to manage highly sensitive government and enterprise data, the requisite foundation of trust must be verifiable. If the origins of the codebase and its licensing compliance remain opaque or demonstrably flawed, it provides external observers and domestic critics with justification to question the OS’s integrity and security posture.
The Critical Security Flaw of Divergence
The greatest technical risk associated with forking a security-hardened project is the creation of a fundamental security flaw known as upstream divergence. When codebases diverge, vulnerabilities discovered and patched in the parent project (GrapheneOS) become increasingly “harder to patch in the downstream (child project) source tree)”.
This implies that BharOS, despite its security focus, risks falling behind on critical security updates. Security patches released for GrapheneOS “might not result in simultaneous security updates being released for BharOS, if at all”. This structural dependency on the research and patching efforts of an external, unaffiliated open-source community defeats the purpose of “digital sovereignty” in the short term, as India’s security posture on these devices remains tethered to the successful maintenance of the upstream project, requiring continuous, complex integration work.
Table 2: The GrapheneOS Allegation: Technical and Ethical Consequences
| Controversy Aspect | Technical Finding | Primary Consequence | Broader Implication |
| Origin of Code | Alleged “cosmetic fork” of GrapheneOS (AOSP derivative). | Questions about the original development effort and internal competency. | Undermines the “indigenous” and “Aatmanirbhar” claims. |
| Licensing | Alleged omission of the GrapheneOS license in the BharOS repository. | Potential legal/licensing violation of open-source requirements. | Challenges the project’s integrity and respect for open source community contributions. |
| Security Assurance | Upstream divergence of the code base makes patching complex. | Vulnerability patching becomes slower and more difficult to implement consistently. | The OS risks falling behind on critical security updates, defeating its core purpose. |
Strategic Placement and Market Realities

The potential of BharOS must be assessed based on its effectiveness in the niche enterprise and government vertical it targets, rather than its capacity to supplant consumer platforms.
The Niche Deployment Strategy and Consumer Barriers
BharOS is narrowly designed for specific high-security, low-volume vertical markets requiring restricted access and closed-group networks. It serves as a specialized, hardened alternative to consumer operating systems for handling extremely sensitive data.
However, this narrow focus creates insurmountable barriers to consumer adoption. Mass deployment would require GMS compatibility for essential services like maps, banking, and general app functionality, which BharOS explicitly lacks. The mandatory reliance on Private App Store Services (PASS) ensures that the platform cannot host the vast number of consumer applications necessary for the typical Indian mobile user. Consequently, the limitations drastically outweigh the privacy advantages for the general public.
The intended function of BharOS is primarily political and strategic: to create a demonstrably secure technological platform that enables the Indian government to enforce future digital governance mandates, such as localized data governance and stringent data residency requirements, without reliance on or friction from foreign technological providers.
Precedents and the Cost of Sovereignty
BharOS is not India’s first endeavor into achieving digital autonomy through domestic operating systems. The Bharat Operating System Solutions (BOSS) Linux, developed by CDAC, previously demonstrated the viability of a government-backed Linux distribution. The history of BOSS Linux, which required security remediation after being targeted by sophisticated threat groups, such as the Pakistan-linked APT36 (Transparent Tribe), highlights that the challenge is not merely development, but perpetual, robust security maintenance and broad organizational adoption.
The cost associated with maintaining an independent operating system is substantial, requiring perpetual investment in security research, vulnerability patching, hardware compatibility testing, and developer support. For a project potentially facing security integrity concerns due to difficulties in integrating upstream patches (the divergence issue), this significant investment could yield diminishing security returns unless the platform achieves reliable, high-volume deployment.
Table 3: BharOS Target Market, Motivators, and Adoption Hurdles
| Area of Analysis | BharOS Position/Goal | Market Reality/Hurdle |
| Target Market | Organizations with stringent privacy/security needs (Government, Defense, Finance). | Extremely limited market volume; high cost of deployment and maintenance. |
| Competition | Alternative to Android/iOS for sensitive tasks. | Cannot offer the GMS ecosystem required for mass consumer adoption. |
| Precedent | Digital sovereignty/Aatmanirbhar Bharat. | Cannot offer the GMS ecosystem required for mass consumer adoption. |
| Ecosystem | Private App Store Services (PASS). | Requires developer investment to vet and tailor apps for a closed ecosystem. |
Geopolitical Context: Data Sovereignty and the Path to Technological Independence

The push for BharOS is rooted in the geopolitical necessity to control national data flows, an issue increasingly central to international relations.
Digital Sovereignty and Risk Mitigation
Loss of control over data flows and data residency is a critical national security risk. By developing a domestic OS, India aims to enforce localized data governance, ensuring that national data remains within its territorial jurisdiction, minimizing exposure to foreign surveillance laws or extraterritorial data requests.
This technological independence also serves as a crucial element of cybersecurity risk mitigation. As cyber threats become geopolitical in nature, developing an OS domestically allows India to control the software supply chain, reducing reliance on external providers and minimizing the risk of remote disablement or surveillance capabilities being embedded within core platforms.
The Policy Balancing Act: Trust and Transparency
The deployment of a state-backed OS inherently introduces a tension regarding potential state surveillance. This tension was recently underscored by the policy debate surrounding the mandatory installation of the state-owned cybersecurity app, Sanchar Saathi. The eventual governmental decision to reverse the mandatory nature of the app, ensuring user choice and the ability to delete the application, was a critical public affirmation of the importance of privacy.
For BharOS to succeed, even in its restricted corporate role, it must demonstrate unequivocally that its architecture (NDA/PASS) is designed to protect user data privacy, not facilitate intrusion. The necessary foundation of trust requires that the root of trust be auditable by independent bodies. The policy shift toward voluntarism regarding state-backed apps softens the broader digital environment, making the adoption of a high-security, voluntary enterprise alternative like BharOS more politically viable.
Furthermore, the architectural principles and technical experience gained from developing BharOS, including kernel hardening, trust chain modifications, and controlled deployment models, are highly transferable. These secure system development practices transcend the mobile domain and can be applied to other critical infrastructure, such as embedded systems or IoT devices, furthering technological independence across numerous sectors.
Recommended Reading

- Operating System Concepts by Abraham Silberschatz, Peter B. Galvin, and Greg Gagne.
- Modern Operating Systems by Andrew S. Tanenbaum and Herbert Bos.
- Linux Kernel Development by Robert Love.
- Data Sovereignty: From the Digital Silk Road to the Return of the State by Anupam Chander and Haochen Sun – An examination of the geopolitical forces, trade regulations, and national policies driving data localization and digital autonomy.
Frequently Asked Questions (FAQ)

Q1: Is BharOS a replacement for Android in the mass consumer market?
A: No. BharOS is not intended as a replacement for Android or iOS for the general public. It is designed and deployed as a secure, high-assurance alternative specifically for organizations and individuals handling sensitive information. Its lack of Google Mobile Services (GMS) and reliance on closed Private App Stores make it unsuitable for typical consumer use.
Q2: Is BharOS an Open Source or Closed Source Operating System?
A: BharOS is built on the Android Open Source Project (AOSP), which is open source. However, the distribution of BharOS developed by JandKops is currently reported to be closed-source. Furthermore, its alleged derivation from GrapheneOS raises complex and unresolved questions about its compliance with open-source licensing mandates.
Q3: Can general consumers download and use BharOS on their phones?
A: Currently, BharOS Services are strictly provided only to organizations that have stringent privacy and security requirements and operate within restricted communication parameters. It is not available for general public download due to its highly specific enterprise focus, the need for organizational vetting of applications via PASS, and the absence of consumer services.
Q4: What are the main security advantages of BharOS over standard Android?
A: The primary architectural advantages are centered around minimizing the attack surface and controlling the software supply chain. BharOS provides security through No Default Apps (NDA), which minimizes the initial surface area for attacks, and Private App Store Services (PASS), which ensures only pre-vetted, organization-approved applications can be installed, preventing high-risk third-party applications.
Conclusion: Sustaining Sovereignty Through Transparency and Audit

BharOS is a significant manifestation of India’s digital sovereignty strategy, offering high architectural advantages (NDA, PASS, NOTA) necessary for secure, high-assurance digital communication environments. The project strategically targets a critical national need: reducing technological dependence on foreign entities for sensitive data handling.
However, the future of BharOS is conditional. The serious, public allegations regarding its non-original source code derivation from GrapheneOS, potential licensing violations, and the resulting risk of slow vulnerability patching (upstream divergence) directly compromise the trust required for any security-focused operating system.
For BharOS to transition from a project of national ambition to a reliably secure national asset, JandKops and IIT Madras must immediately establish verifiable trust through transparent action:
- Compliance and Disclosure: The developers must publicly clarify the relationship between BharOS and GrapheneOS and immediately adhere to all relevant open-source licensing requirements.
- Mandatory Audits: The codebase must be subjected to mandatory, independent security audits by recognized, neutral national or international experts. The security advantages must be “backed with evidence, which can be independently analysed and verified by experts,” moving beyond promotional claims.
- Patching Commitment: Clear, published protocols must be established to demonstrate an ongoing, robust capacity for timely patching of vulnerabilities identified in the upstream AOSP and GrapheneOS source trees, effectively addressing the critical risk of divergence.
BharOS represents a vital step toward digital self-reliance. Its long-term credibility, however, rests entirely on establishing an unimpeachable, transparent, and auditable technical foundation, ensuring the platform is reliable as well as domestically developed.




















Leave a Reply